Findings of the detector that identify an anomaly in the same file and method as the known misuse.
| Hit |
Rank |
Confidence |
Confidence String |
Pattern Support |
Pattern Violation |
Target Environment Mapping |
|
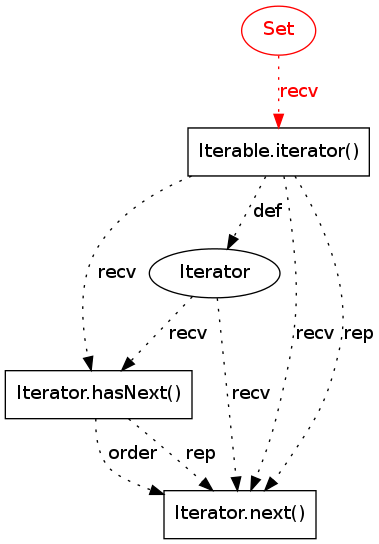
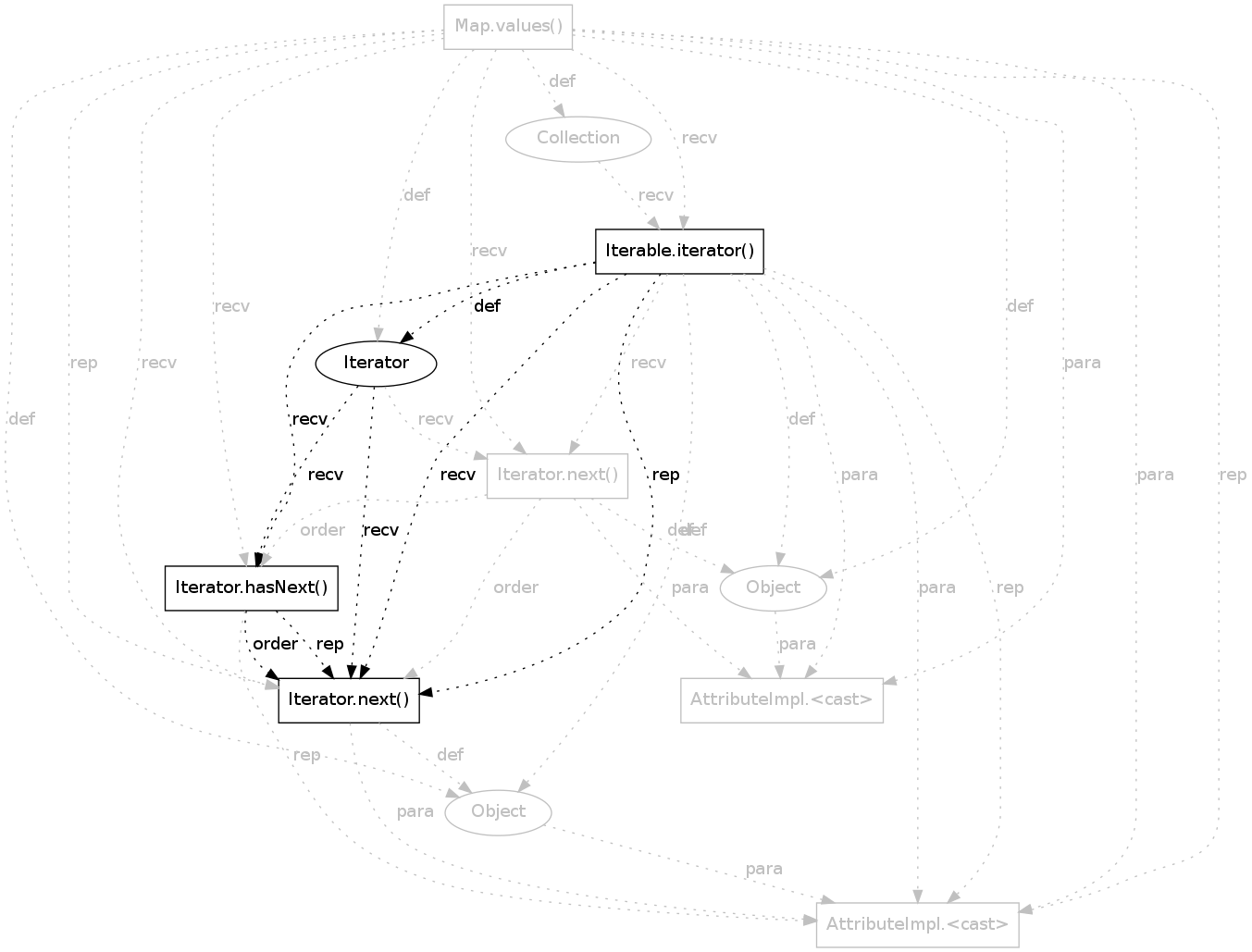
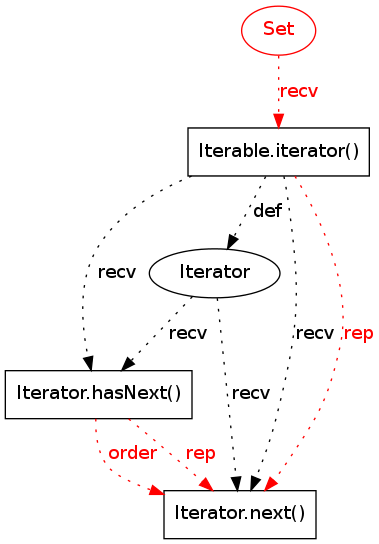
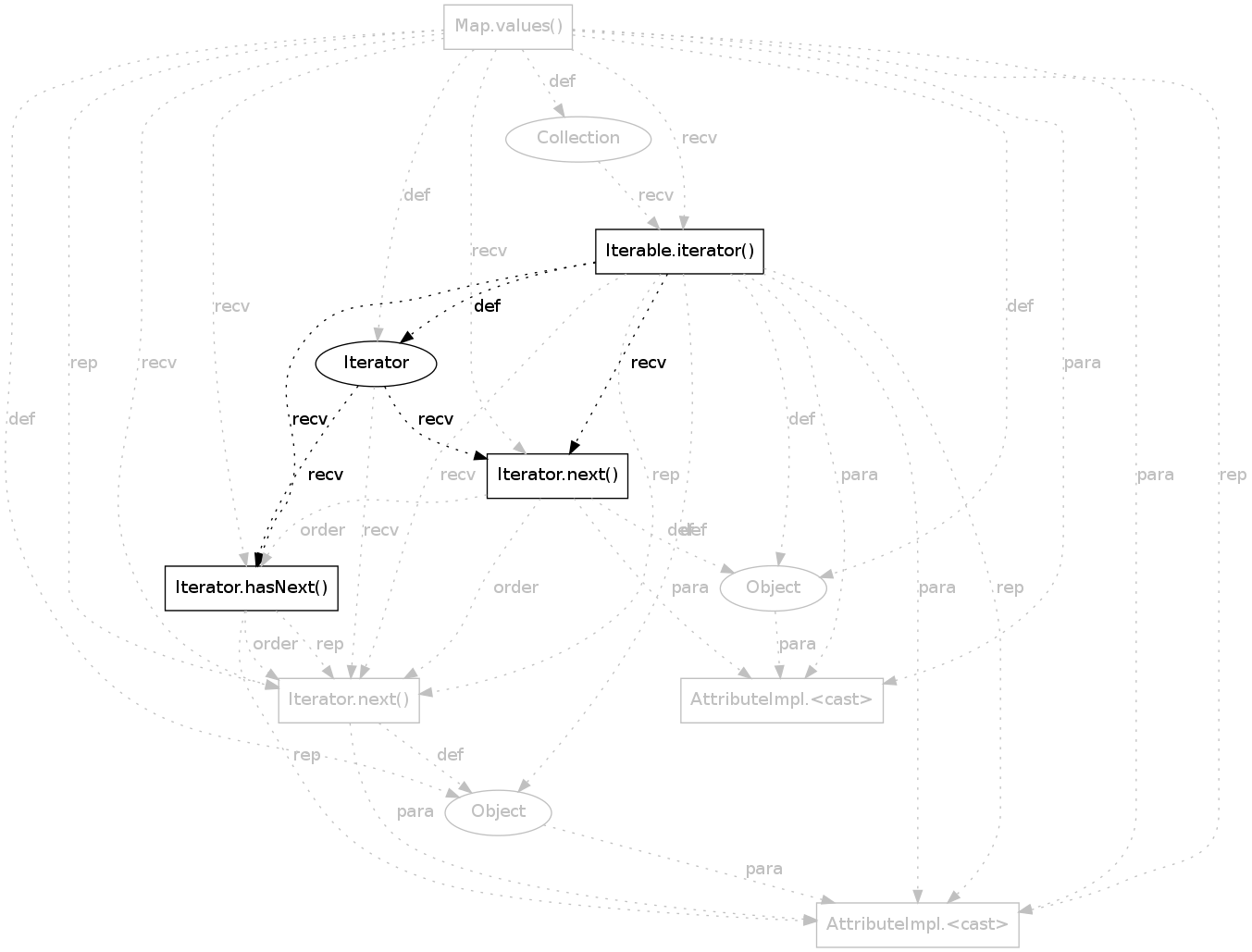
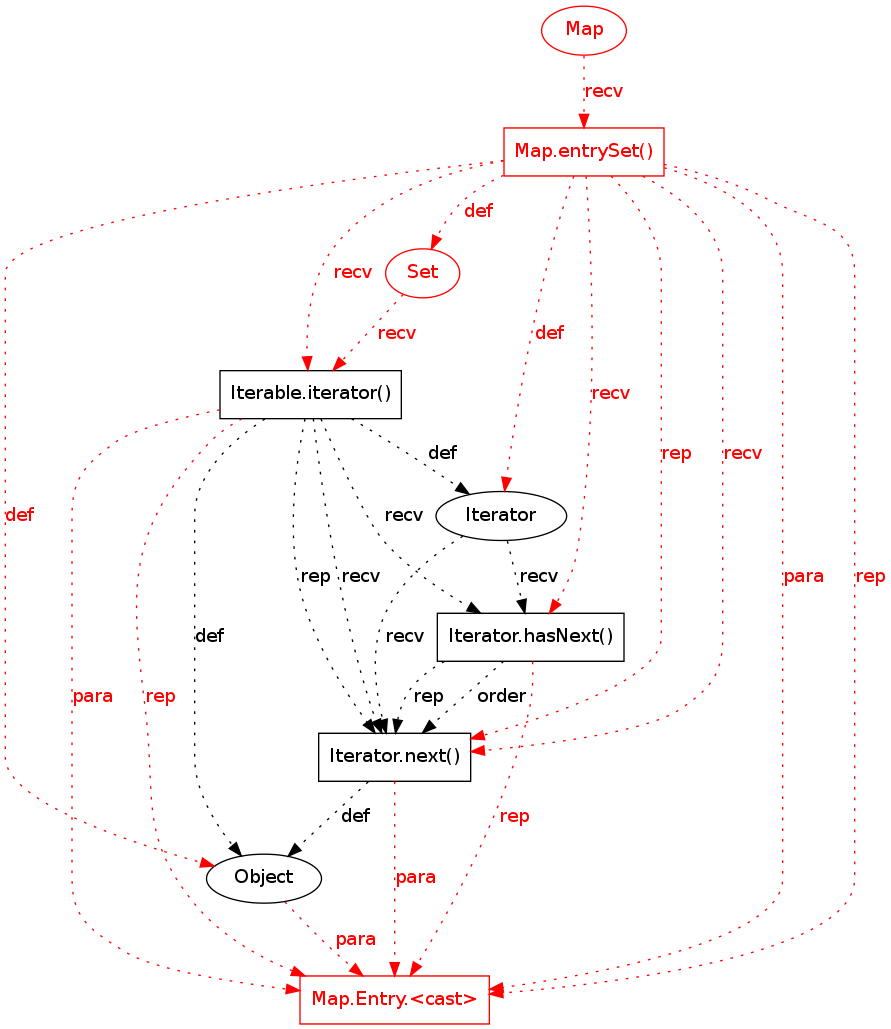
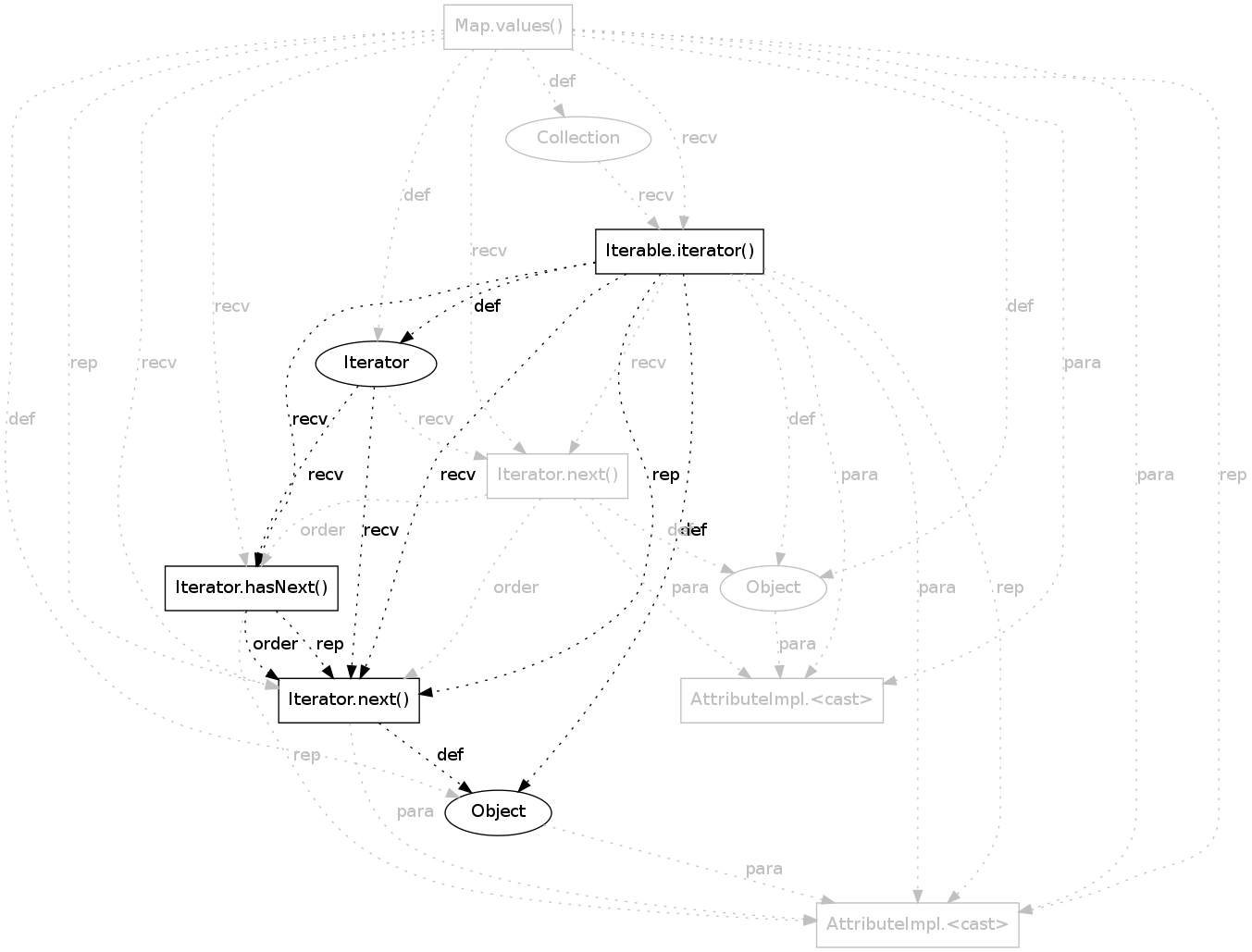
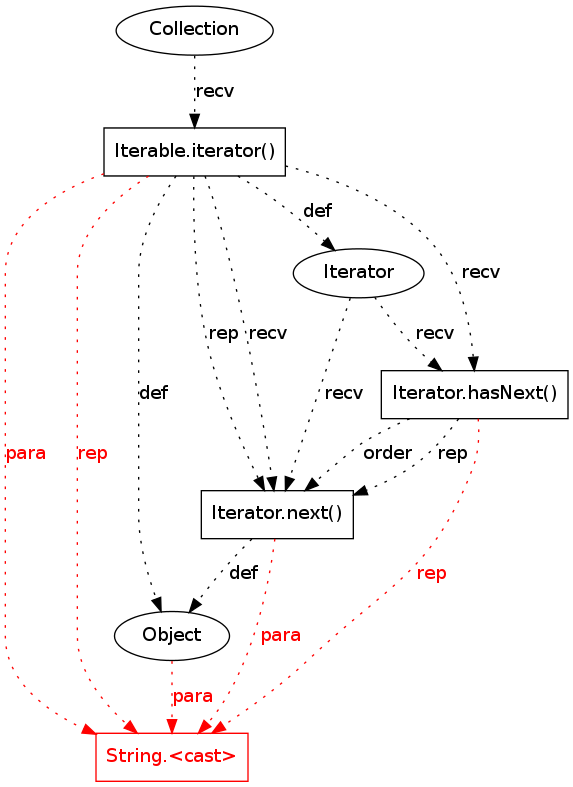
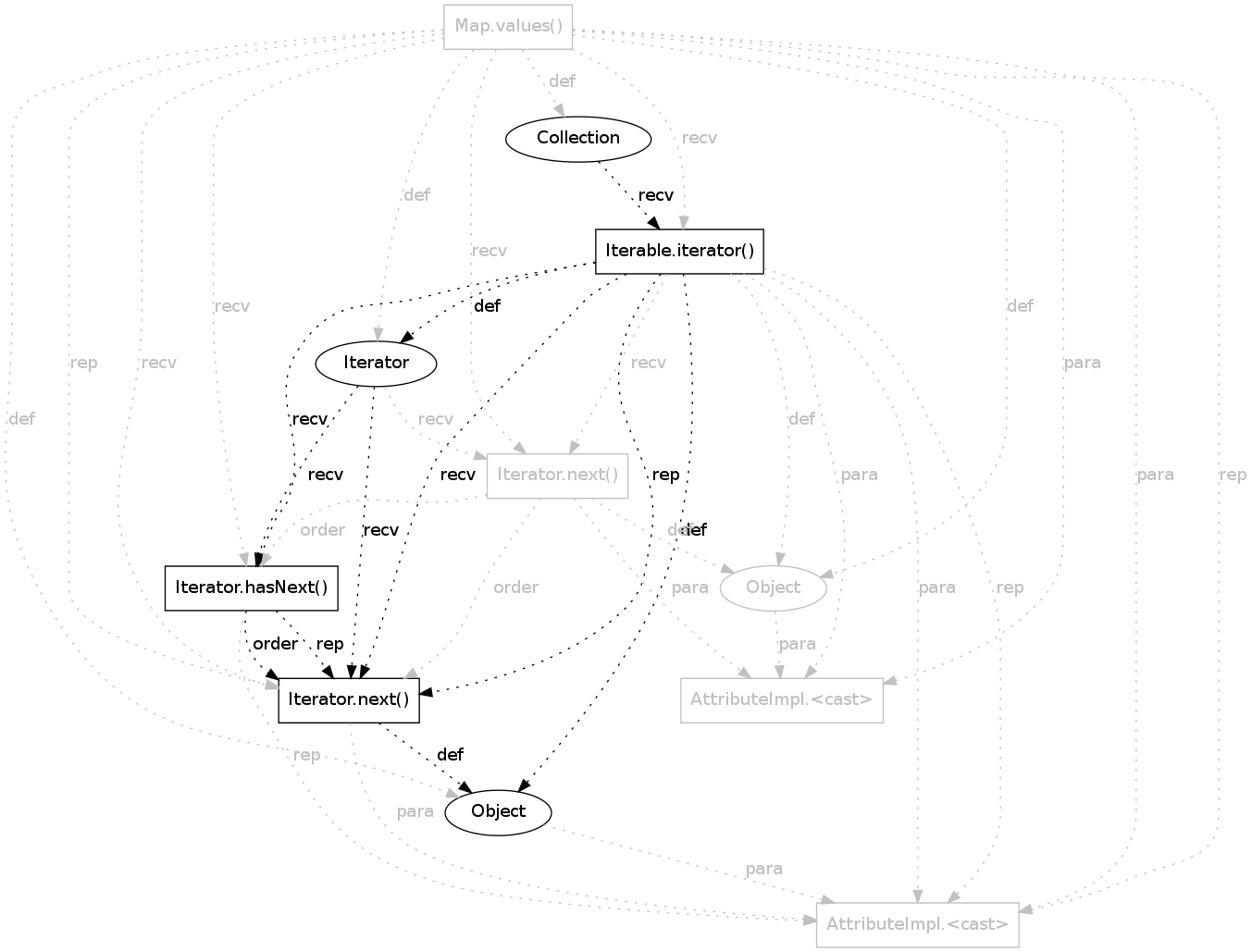
?
|
113 |
0.4665256 |
((pattern support = 16 / 495)(pattern violations = 1 / 130)(violation support = 1 / 1)(overlap = 1 - (4 / 23))) / 4 |
16 |
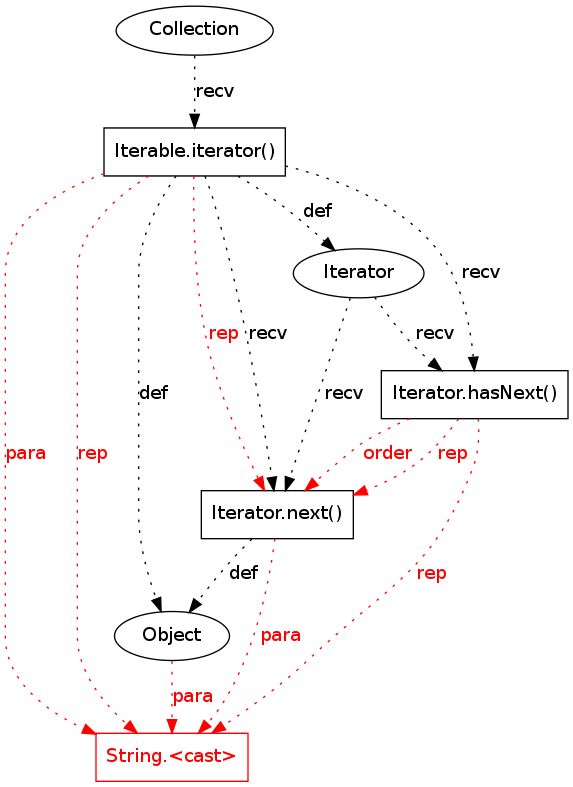
|
|
|
?
|
129 |
0.4574495 |
((pattern support = 11 / 495)(pattern violations = 1 / 132)(violation support = 1 / 1)(overlap = 1 - (7 / 35))) / 4 |
11 |
|
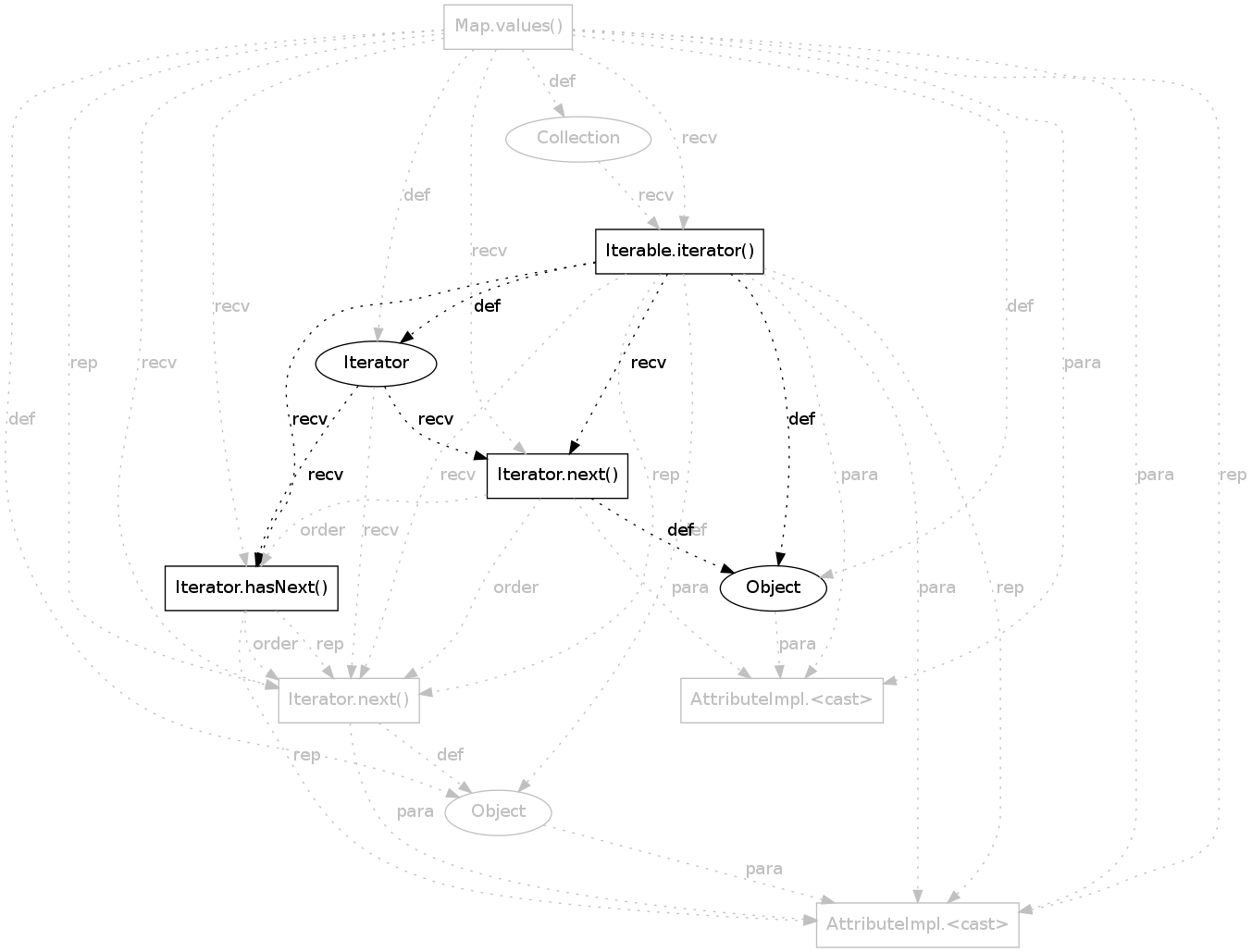
|
|
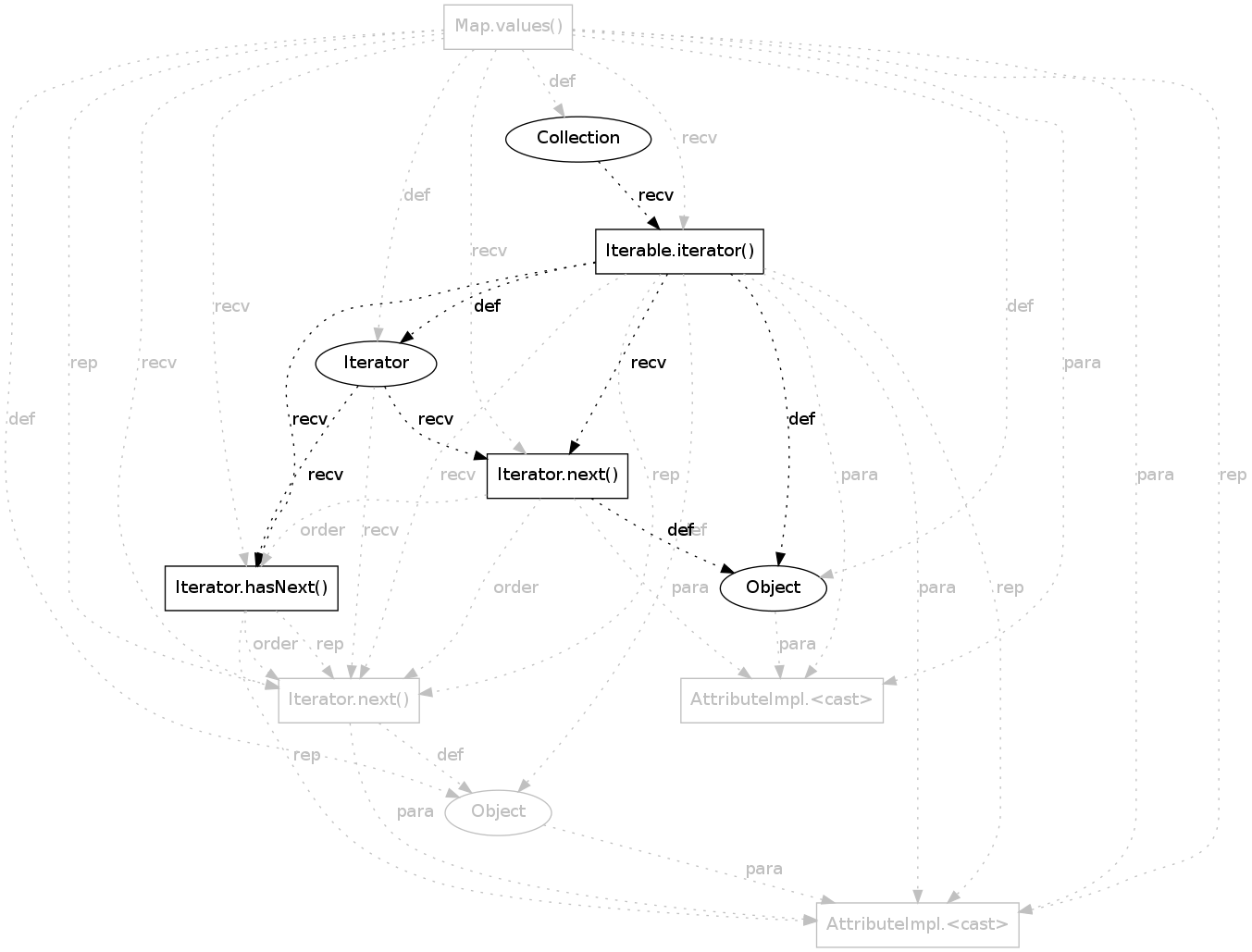
?
|
1352 |
0.24543367 |
((pattern support = 16 / 495)(pattern violations = 1 / 107)(violation support = 1 / 87)(overlap = 1 - (1 / 14))) / 4 |
16 |
|
|
|
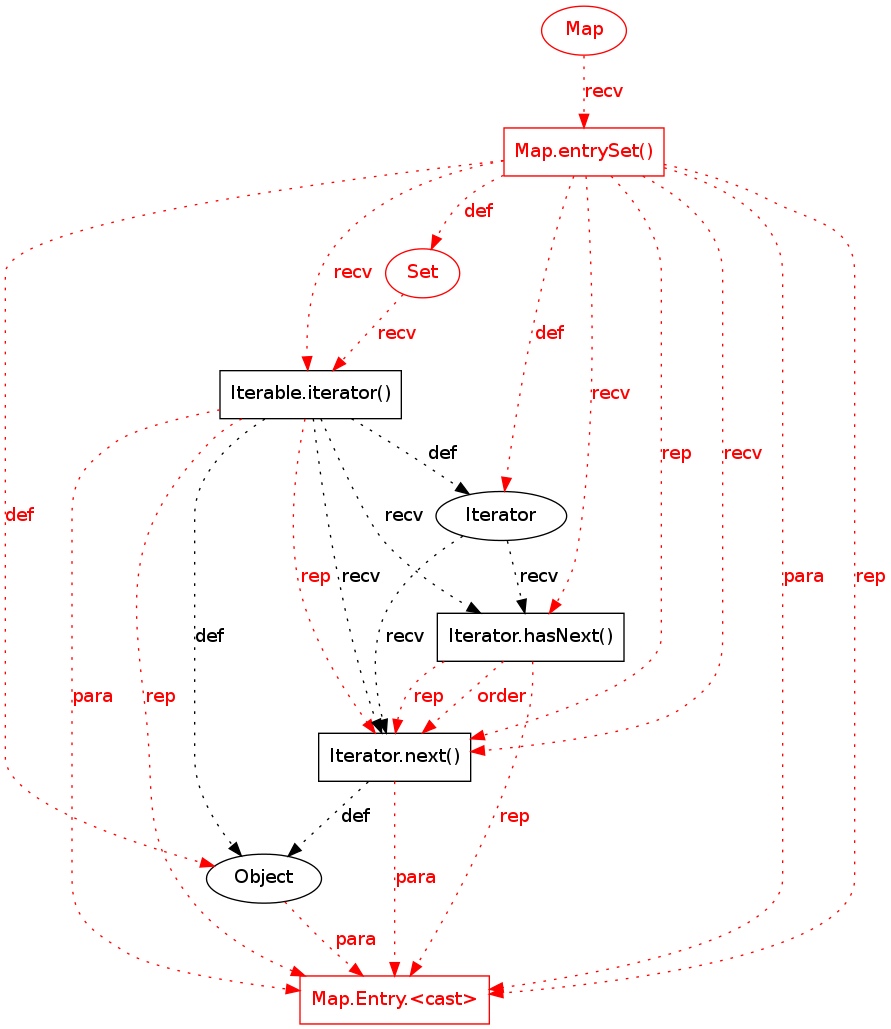
?
|
154 |
0.4389887 |
((pattern support = 16 / 495)(pattern violations = 1 / 107)(violation support = 1 / 1)(overlap = 1 - (4 / 14))) / 4 |
16 |
|
|
|
?
|
2032 |
0.23200306 |
((pattern support = 11 / 495)(pattern violations = 1 / 132)(violation support = 1 / 80)(overlap = 1 - (4 / 35))) / 4 |
11 |
|
|
|
?
|
754 |
0.26475933 |
((pattern support = 16 / 495)(pattern violations = 1 / 130)(violation support = 1 / 16)(overlap = 1 - (1 / 23))) / 4 |
16 |
|
|